How to Improve WordPress Security Against DDoS: Arizona Host
If your WordPress site serves patients, clients, or customers, even short outages erode trust and revenue. How to Improve WordPress Security Against DDoS is a practical mix of architecture, managed services, and operational playbooks that keeps regulated sites online and compliant.
Summary
This guide explains practical steps to harden WordPress against distributed denial-of-service attacks, from network-level mitigation to application hardening and incident response. You will get an actionable checklist, recommended service layers, and compliance-minded choices for healthcare, legal, and financial sites hosted in Arizona.
Why DDoS protection matters for regulated businesses
Downtime hits revenue and compliance at once. Healthcare or financial websites that process protected data must avoid outages that could interrupt patient access or transactional systems. Layered DDoS defenses reduce the chance of region-wide downtime and support recovery SLAs required for HIPAA and SOC 2 programs.
Core layers to stop DDoS attacks
1) Edge mitigation and CDN
Move traffic to an edge provider that offers always-on, global DDoS mitigation and caching. A CDN plus edge scrubbing spreads incoming traffic globally and absorbs volumetric floods, reducing load on your origin. Providers like Cloudflare offer adaptive and layer 3/4/7 mitigation that protects WordPress without complicated origin changes. Use a CDN to cache public pages and offload requests from the origin.
2) Managed Web Application Firewall (WAF)
A managed WAF filters malicious HTTP requests before they reach WordPress. Configure rules to block common WordPress attack patterns, rate-limit suspicious endpoints such as XML-RPC and login pages, and enable bot-challenge or CAPTCHA for abusive request sources. A managed WAF reduces application-layer (layer 7) DDoS impact while preventing exploit attempts.
3) Network-level protections and scrubbing
For large volumetric attacks, you need an ISP or data center partner with scrubbing capabilities and sufficient bandwidth. Colocation or managed hosting in a partner facility that offers advanced DDoS scrubbing gives you on-net protection and faster mitigation. Consider colocating critical origins regionally to reduce latency and keep data within Arizona when compliance or performance matters. Explore Colocation options with local support for rapid response.
4) Harden WordPress configuration
- Disable or restrict XML-RPC if you do not use it. XML-RPC is often abused in DDoS and brute-force campaigns.
- Rate-limit and block suspicious IPs at the server level with fail2ban or similar tools. Implement system-level throttling for login and search endpoints.
- Enforce strong passwords and mandatory MFA for all admin accounts. Use role-based access and least privilege for plugins and users.
- Keep the core, themes, and plugins updated in staging-first workflows to avoid regressions.
These changes reduce the attack surface and keep the site resilient when volumetric pressure lands at the origin.
5) Auto-scaling, graceful degradation, and caching
If your hosting environment supports auto-scaling, configure it to grow capacity during legitimate traffic spikes. For static or semi-static pages, tune caching aggressively and serve stale-while-revalidate to avoid origin thrashing. For highly regulated environments, prefer managed private cloud or secure WordPress hosting with tested scaling strategies that preserve compliance and logging.
6) Redundancy, backups, and recovery playbooks
Daily snapshots, off-site backups, and tested restore processes are non-negotiable. Maintain a documented incident response playbook that includes failover origin, DNS TTL plans, and escalation contacts. Test your restore and failover regularly to meet compliance evidence requirements.
Operational and policy controls
Logging and monitoring
Centralize logs from WAF, CDN, web server, and OS. Use alerting to detect abnormal request rates, error spikes, or resource exhaustion. Retain logs in a tamper-resistant store to support post-incident forensics and compliance audits.
Access controls and change management
Apply least privilege, multi-factor authentication, and strong change control for plugin installation or site configuration changes. Use staging environments for updates and rollback strategies to avoid accidental exposure during maintenance windows.
Vendor and SLA selection
Choose edge and hosting partners that publish mitigation SLAs, offer 24/7 support, and maintain capacity for volumetric attacks. For regulated organizations, verify compliance alignment and evidence availability when selecting managed WordPress hosting or colocation providers.
Quick actionable checklist
- Enable an edge CDN with always-on DDoS mitigation and rate limiting.
- Put a managed WAF in front of WordPress and tighten rules for login, REST API, and XML-RPC.
- Block or throttle abusive IPs and user-agents at the edge and origin.
- Enforce MFA, least privilege, and regular patching for core and plugins.
- Maintain daily backups, off-site snapshots, and a tested restore plan.
- Monitor traffic volumes and errors with centralized alerting and runbooks.
- Consider colocating critical infrastructure for low-latency and regional control.
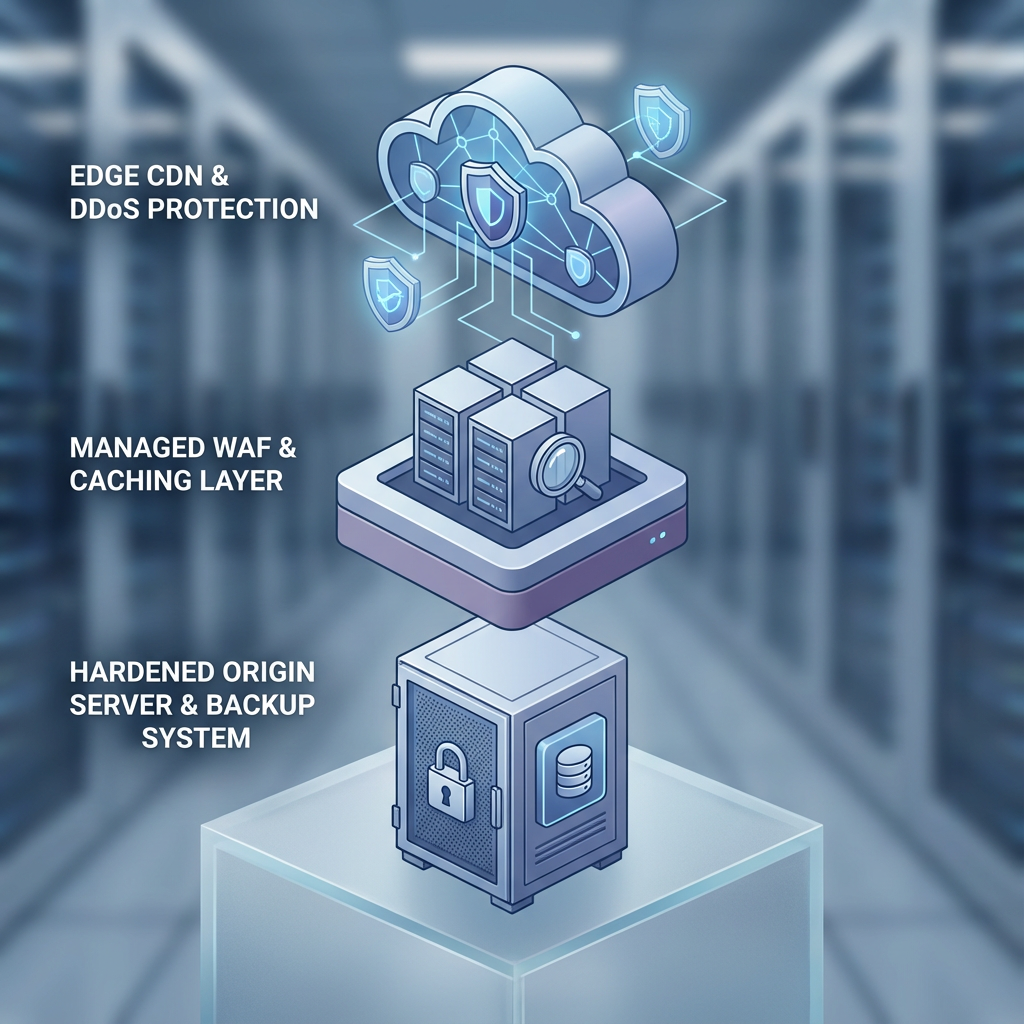
Example architecture for regulated WordPress sites
Use a CDN and WAF at the edge for layer 3/4/7 mitigation, deploy origin servers in a managed, HIPAA-ready private cloud or colocation facility, and run backups and failover inside the same compliance boundary. Armour Cloud’s Secure WordPress Hosting and HIPAA Compliant Managed Cloud Hosting combine these elements with 24/7 support and regional data center options to simplify compliance and uptime.
When to call the experts
If you face repeated application-layer floods, or if your organization must preserve strict data residency and audit trails, engage a provider who can manage the stack end to end. Armour Cloud provides secure managed WordPress hosting, DDoS mitigation integration, and regional colocation to maintain performance, compliance, and uptime. Call (602) 529-3435 or visit the contact page to request a consultation.
Frequently Asked Questions
How quickly can DDoS protection be turned on for a WordPress site?
Edge-based protections are often enabled within minutes by changing DNS to point at the CDN or edge provider. Complex managed WAF policies and origin firewall tuning can take additional hours depending on traffic patterns.
Will a CDN slow down my site if it's under attack?
No, a properly configured CDN typically improves performance. During attacks, the CDN serves cached content and absorbs malicious traffic, keeping your origin responsive for legitimate users.
What parts of WordPress are most targeted in DDoS attempts?
Login pages, xmlrpc.php, REST API endpoints, and expensive dynamic pages that bypass cache are common targets. Rate-limiting and WAF rules help protect these endpoints.
Do I need to change hosting providers to get DDoS protection?
Not always. You can layer a CDN and WAF in front of your existing host. However, for very large attacks or compliance needs, moving to a host with on-net scrubbing and regional colocation may be advantageous.
Can Armour Cloud help with both DDoS mitigation and HIPAA compliance?
Yes. Armour Cloud combines secure WordPress hosting, HIPAA-compliant managed cloud options, and 24/7 support to protect regulated workloads while meeting audit and evidence requirements.
Next steps and support
If you want a fast assessment of your WordPress setup and DDoS readiness, request a consultation. Armour Cloud offers secure managed WordPress hosting tailored to regulated organizations, plus colocation and managed M365 services to cover surrounding systems. Call (602) 529-3435 for secure hosting or compliance support, or request a consultation online.
Conclusion
Here’s the thing, defending WordPress from DDoS is not a single tool, it is a layered strategy that blends edge mitigation, a managed WAF, origin hardening, and rigorous operations. For healthcare, finance, and legal teams that require compliance and uptime, combining local hosting or colocation with a proven edge provider and a managed WordPress platform provides the best balance of resilience and control. If you operate in Arizona and need regional, compliant hosting and managed DDoS defenses, Armour Cloud can help.
About Armour Cloud
Armour Cloud is a Phoenix-based provider of secure, compliant cloud hosting and managed IT solutions for regulated industries. Armour Cloud delivers high-performance infrastructure built on Arizona data centers, offering low-latency, HIPAA-compliant hosting with 24/7 support.
We specialize in helping healthcare, finance, and legal organizations protect sensitive data, meet compliance requirements, and modernize their IT with scalable, managed cloud environments.
Our Top Services:
- Colocation
- Managed Desktop-as-a-Service (VDI)
- Managed Microsoft 365 Services
- Email Security & Encryption
- Secure WordPress Hosting
- Private Cloud Hosting
- HIPAA Compliant Cloud Solutions
Ready to Secure Your Cloud?
📞 Call (602) 529-3435 or Contact Armour Cloud to get started with a free consultation.




